Imagine you receive an email or a text message from your bank or your favorite online shopping website asking you to urgently verify your personal information or reset your password.
You click on the link provided, enter your details, and feel relieved that everything is back to normal. But what if that email wasn’t actually from your bank or your favorite shopping website but rather from a cybercriminal trying to steal your personal information?
This type of online scam, known as phishing, is becoming increasingly common and sophisticated, putting individuals and businesses at risk of identity theft, financial fraud, and other cybersecurity threats.
In this article, we’ll understand what phishing is, different phishing techniques, and what you can do to protect yourself from becoming a victim.
Phishing: Definition
Phishing is a type of online scam where a cybercriminal tries to trick you into sharing your personal information or login credentials by pretending to be a trustworthy source, like a bank, an online store, or a government agency.
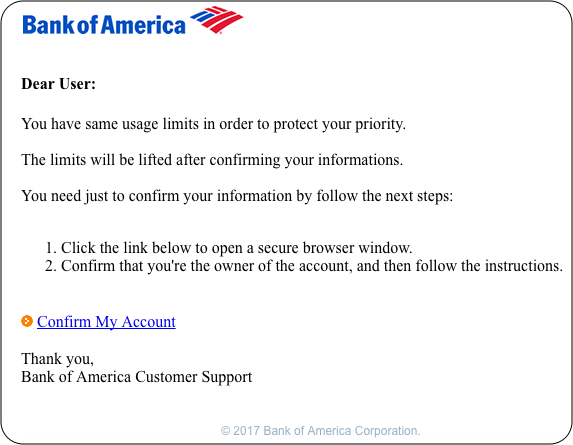
For example, you might receive an email that looks like it’s from your bank, asking you to click on a link and enter your username and password to verify your account. The email might look real and use official logos and graphics to make it seem legitimate, but in reality, it’s a fake message designed to steal your information.
Phishing attacks can also happen through phone calls, text messages, or social media messages. They often use urgency or fear to pressure you to take action quickly without thinking.
The danger of falling for a phishing scam is that cybercriminals can use your stolen information to access your accounts, steal your money, or even steal your identity.
Types of Phishing Attacks
There are several types of phishing attacks, and they all work differently to trick you into giving away your personal information or login credentials.
The following are some of the most common types of phishing attacks:
- Email Phishing: This is when a cybercriminal sends you an email that looks like it’s from a trusted source, such as a bank or an online store, asking you to click on a link and enter your personal information. They may also attach a malicious file to the email that can infect your computer with malware.
- Spear Phishing: This is a more targeted form of phishing where the attacker gathers information about you, such as your name, job title, or recent activities, to make the message seem more convincing. For example, they might send you an email that looks like it’s from your boss, asking you to transfer money to a specific account.
- Smishing: This is when a phishing attack happens through a text message instead of an email. The message might ask you to call a specific number or click on a link to verify your account information.
- Vishing: This is when a phishing attack happens over the phone. The attacker might pretend to be a representative from a trusted organization, such as your bank, and ask you to provide your account details or personal information.
- Whaling: This is a type of spear phishing that targets high-profile individuals, such as CEOs or politicians. The attacker might create a fake email from a senior executive or a government agency and ask for sensitive information or request a wire transfer.
It’s important to be aware of these different types of phishing attacks and to take precautions, such as not clicking on suspicious links or providing personal information to unknown sources.
Common Features of Phishing Attacks
Phishing attacks can come in many forms, but they often share some common features that can help you recognize and avoid them.
Below are a few things to watch out for:
- Urgency: Phishing emails often create a sense of urgency or fear to get you to act quickly without thinking things through. For example, they might say that your account has been compromised and that you need to reset your password immediately.
- Suspicious links: Phishing emails often contain links that lead to fake websites that steal your personal information or install malware on your computer. These links might look legitimate, but if you hover your mouse over them, you can often see the actual URL.
- Requests for personal information: Phishing emails often ask for personal information, such as your login credentials, credit card numbers, or social security number. Legitimate organizations will never ask for this information via email.
- Poor spelling and grammar: Phishing emails are often poorly written and contain spelling and grammar mistakes. This is because the attackers may not be native English speakers.
- Suspicious attachments: Phishing emails may contain attachments that are infected with malware. If you’re not expecting an attachment or if it looks suspicious, don’t download or open it.
- Spoofed sender addresses: Phishing emails may appear to come from a legitimate organization or a trusted source, but if you look closely at the sender’s email address, you may notice that it’s slightly different or misspelled.
By keeping an eye out for these common features, you can protect yourself from falling victim to a phishing attack.
How To Prevent Phishing Attacks?
Phishing attacks can be difficult to detect, but you can take the following steps to prevent them from happening.
Keep your software up-to-date
Make sure that your computer’s operating system, web browser, and anti-virus software are all up-to-date. This can help protect against known vulnerabilities and malware.
Be cautious of suspicious emails
If you receive an email that asks for personal information or contains a suspicious link or attachment, don’t click on anything. Instead, contact the organization directly through their official website or phone number to confirm whether the message is legitimate.
Look for secure websites
When you’re on a website that requires you to enter personal information, look for the “https” at the beginning of the URL and the padlock icon in the address bar. This indicates that the site is using a secure connection.
Use strong passwords
Create unique passwords for each of your online accounts and use a combination of upper- and lower-case letters, numbers, and symbols. Avoid using personal information or easy-to-guess phrases. We recommend using our Password Generator tool if you need help with having a strong password.
Enable multi-factor authentication
Many websites and apps offer multi-factor authentication, which requires you to enter a code sent to your phone in addition to your password. This adds an extra layer of security to your accounts.
Educate yourself
Stay informed about the latest phishing tactics, and be wary of unexpected messages or requests for personal information. You can also take online courses or attend cybersecurity training to learn more about how to protect yourself.
Conclusion
Phishing attacks are a serious threat to your online security and can lead to the theft of personal information, financial loss, and identity theft.
However, by staying attentive and taking preventative measures, we can reduce our risk of being targeted by cybercriminals.
Remember, it’s important always to be skeptical of unexpected messages or requests for personal information and verify the sender’s legitimacy before clicking on any links or providing sensitive information.
By following these guidelines and staying informed, you can enjoy a safer and more secure online experience.
